The High-Stakes Crisis: Why Tech Giants are Losing the War Against Counterfeit Hardware
Executive Summary
The electronics and hardware industry is currently navigating a systemic crisis that threatens the very foundation of digital infrastructure. In 2026, counterfeiting has transcended simple trademark infringement, evolving into a complex web of sub-standard components and gray-market infiltration. For tech giants, the risk is no longer just a dip in quarterly revenue; it is a matter of catastrophic product failure, legal liability, and the erosion of consumer trust. This article explores the macroeconomic impact of hardware counterfeiting, the dangerous limitations of legacy auditing, and the necessary shift toward automated, intelligent brand sovereignty. We examine why the tech sector requires a specialized defensive posture to survive an increasingly sophisticated illicit economy.
The Silent Infiltration of the Global Tech Supply Chain
In the high-velocity world of electronics, innovation is the primary currency. However, as hardware becomes more complex, the supply chains supporting it have become increasingly opaque. For a global tech giant, a single device may contain thousands of components sourced from hundreds of different suppliers across multiple continents. This complexity is the perfect breeding ground for counterfeiters.
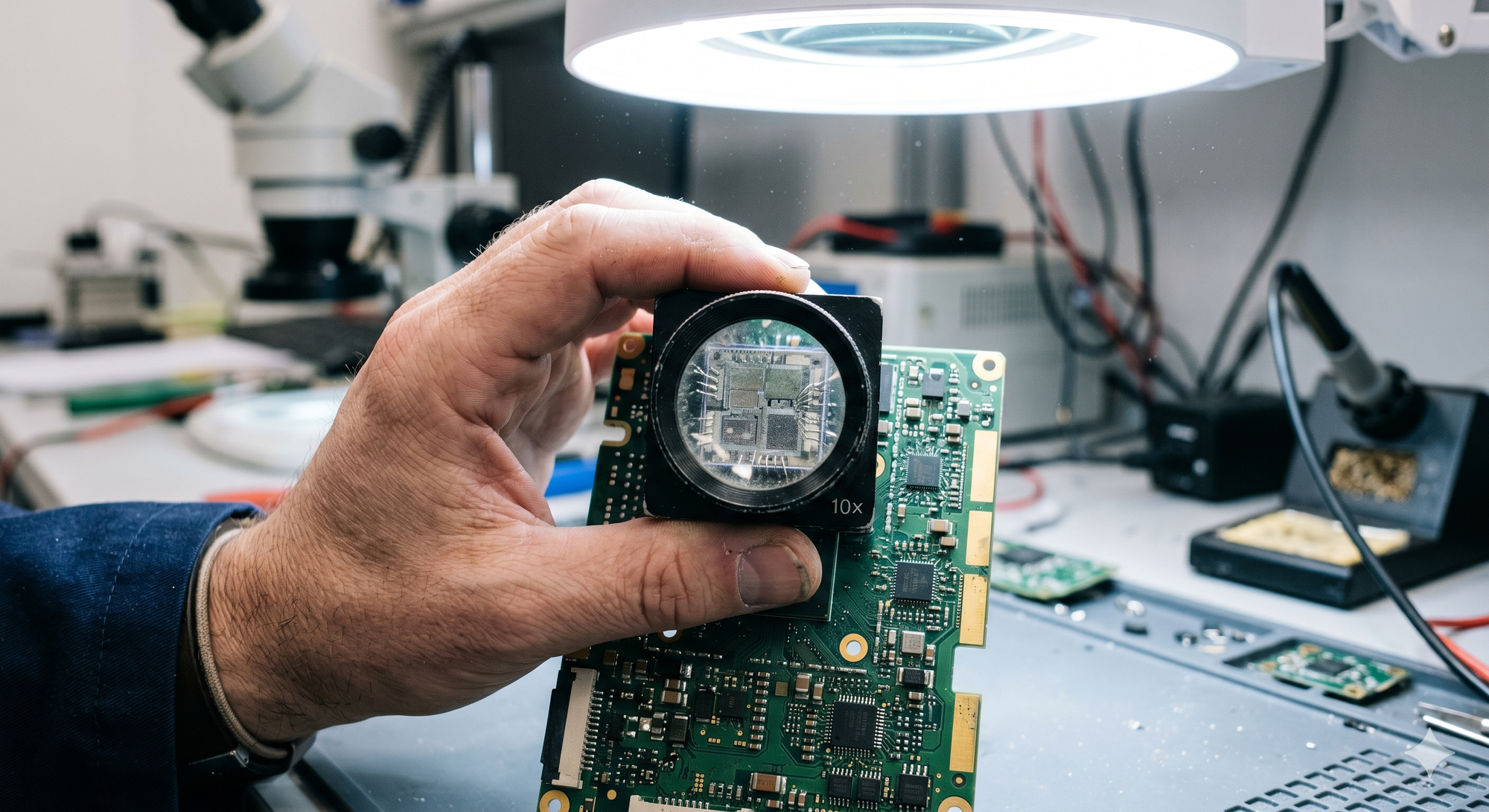
The modern counterfeit hardware problem isn't just about "fake phones." It’s about the silent infiltration of sub-standard semiconductors, refurbished capacitors sold as new, and unverified peripheral components. When these "poison pills" enter the ecosystem, the brand owner is the one left holding the liability. The shift from localized illicit markets to a global, digitally-enabled shadow economy has made traditional oversight impossible.
Beyond Revenue: The Liability of "Good Enough" Electronics
In most industries, a counterfeit product is a disappointment. In the electronics and hardware sector, counterfeits pose a hazard. This is where the "Tech Giant" faces a unique set of challenges that apparel or luxury brands do not.
The Safety and Fire Hazard Reality
A counterfeit lithium-ion battery or a sub-standard power adapter is a ticking time bomb. Every year, thousands of electrical fires and device explosions are traced back to unauthorized components that bypass rigorous safety certifications like UL or CE. When a flagship device catches fire, the public doesn't blame the anonymous counterfeiter on an encrypted messaging app; they blame the logo on the device.
The Medical and Industrial Fallout
Hardware counterfeiting extends into critical infrastructure. Counterfeit components in medical imaging equipment, automotive sensors, or aerospace hardware don't just lead to "bad reviews"—they lead to loss of life. For enterprise-level hardware providers, a single counterfeit-induced failure can cost billions of dollars in recalls and litigation.
What are the primary risks of counterfeit electronics for tech companies?
The primary risks include catastrophic product failure (fires, explosions), massive legal liability, irreversible brand damage, and the loss of critical consumer trust. Unlike other sectors, counterfeit electronics pose significant public safety risks, making the eradication of fakes a matter of corporate compliance and consumer safety rather than just a marketing concern.
The "Whack-a-Mole" Trap: Why Legacy Auditing is Failing
For decades, the standard response to counterfeiting was a combination of manual marketplace monitoring and occasional factory audits. In the context of 2026, these methods are not only outdated—they are a drain on corporate resources that provide a false sense of security.
The Latency Problem
Manual brand protection is inherently reactive. By the time a human analyst identifies a suspicious listing or a rogue distributor, thousands of units have already been shipped. In the electronics sector, where product life cycles are measured in months, this latency is fatal. The counterfeiter has already made their profit and moved on to the next SKU before the first cease-and-desist letter is even drafted.
The Scalability Paradox
As tech giants expand their portfolios—adding IoT devices, wearables, and enterprise hardware—the surface area for attack grows exponentially. A manual team that was effective five years ago is now drowned in a sea of data. You cannot solve a machine-scale problem with human-scale solutions. This "Whack-a-Mole" approach leads to a high "cost-per-takedown" with virtually zero impact on the overall availability of fakes.
The Economic Impact: Quantifying the "Ghost Market"
To understand the scale of the threat, one must look at the macroeconomic data surrounding the electronics sector. The illicit trade in tech goods is no longer a fringe activity; it is a sophisticated industry with its own R&D, logistics, and marketing arms.
- Market Dilution: Counterfeit goods represent a direct diversion of revenue, but they also cause price erosion in legitimate channels as authorized retailers struggle to compete with "too-good-to-be-true" prices.
- Customer Churn: 65% of consumers who unknowingly purchase a counterfeit electronic device will lose trust in the original brand, regardless of who was at fault.
- Support Burden: Tech companies often spend millions on customer support and warranty claims for products that turn out to be fakes, further straining the bottom line.
How does counterfeiting affect the ROI of tech R&D?
Counterfeiting directly cannibalizes the ROI of R&D by allowing illicit actors to profit from a brand’s innovation without incurring the costs of development, testing, or safety certification. This price suppression forces legitimate brands to lower margins, ultimately reducing the capital available for future technological breakthroughs.
The Strategic Shift: From Protection to Market Sovereignty
The failure of traditional methods has necessitated a paradigm shift. Leading hardware companies are moving away from the concept of "protecting" their brand and toward the concept of Market Sovereignty.
Market sovereignty means having total visibility and control over where your brand appears and how your products are sold across the entire digital landscape. This isn't achieved through more lawyers; it's achieved through Automation and Intelligence.
The Need for "Always-On" Awareness
In an environment where a new counterfeit listing can appear every few seconds, defense must be continuous. The goal is to create a digital environment that is "hostile" to counterfeiters. When the cost of infringing on a specific brand becomes too high—due to instant detection and automated enforcement—counterfeiters naturally gravitate toward easier targets.
Data-Driven Decision Making
The modern Chief Security Officer (CSO) needs more than just a list of removed links. They need intelligence on who the major players are, where the traffic is being diverted, and how much revenue is being reclaimed. This high-level oversight allows brand protection to move from a "legal expense" to a "revenue recovery" department.
The Future of Hardware Authenticity
As we look toward the remainder of 2026 and beyond, the battle for hardware authenticity will only intensify. The emergence of highly convincing "super-fakes"—products that are visually indistinguishable from the original even to trained eyes—means that brands must rely on data patterns and behavioral intelligence rather than just visual inspection.
The tech giants of tomorrow will be those that view brand integrity as an integral part of their product engineering. A secure product is not just one that works; it can be verified as authentic in every corner of the digital and physical world.
Why is automation essential for electronics brand protection?
Automation is essential because it matches the scale and speed of modern counterfeiters. It allows for real-time monitoring across millions of data points, identifies illicit networks instead of individual listings, and initiates enforcement actions faster than manual teams, thereby minimizing the window of opportunity for counterfeiters to harm consumers.
Securing the Digital Frontier
The electronics industry stands at a crossroads. The legacy methods of the past are no longer sufficient to guard against the automated threats of the present. For the tech giant, the path forward is clear: embrace intelligence, automate defense, and reclaim the revenue that is rightfully yours.
The integrity of your brand is your most valuable asset. In an age of digital shadows, ensuring that your customers receive the quality and safety they expect is not just a business strategy—it is a moral and legal imperative. It is time to move beyond the circuit board and secure the entire ecosystem.
Is your brand truly protected, or are you just playing the "Whack-a-Mole" game?
The future of your market share depends on the answer.
Resources
- Global Tech Security Alliance (GTSA). (2025). Macroeconomic Trends in Hardware Infringement.
- Harvard Business Review. (2026). The Hidden Costs of Supply Chain Infiltration in the Electronics Sector.
- International Intellectual Property Institute (IIPI). (2024). Safety Risks and Liability in Counterfeit Consumer Electronics.
- World Economic Forum (WEF). (2025). The Future of Digital Trust and Authenticity in Global Commerce.