Securing Your Digital Gateway: The Definitive Guide to Domain Protection
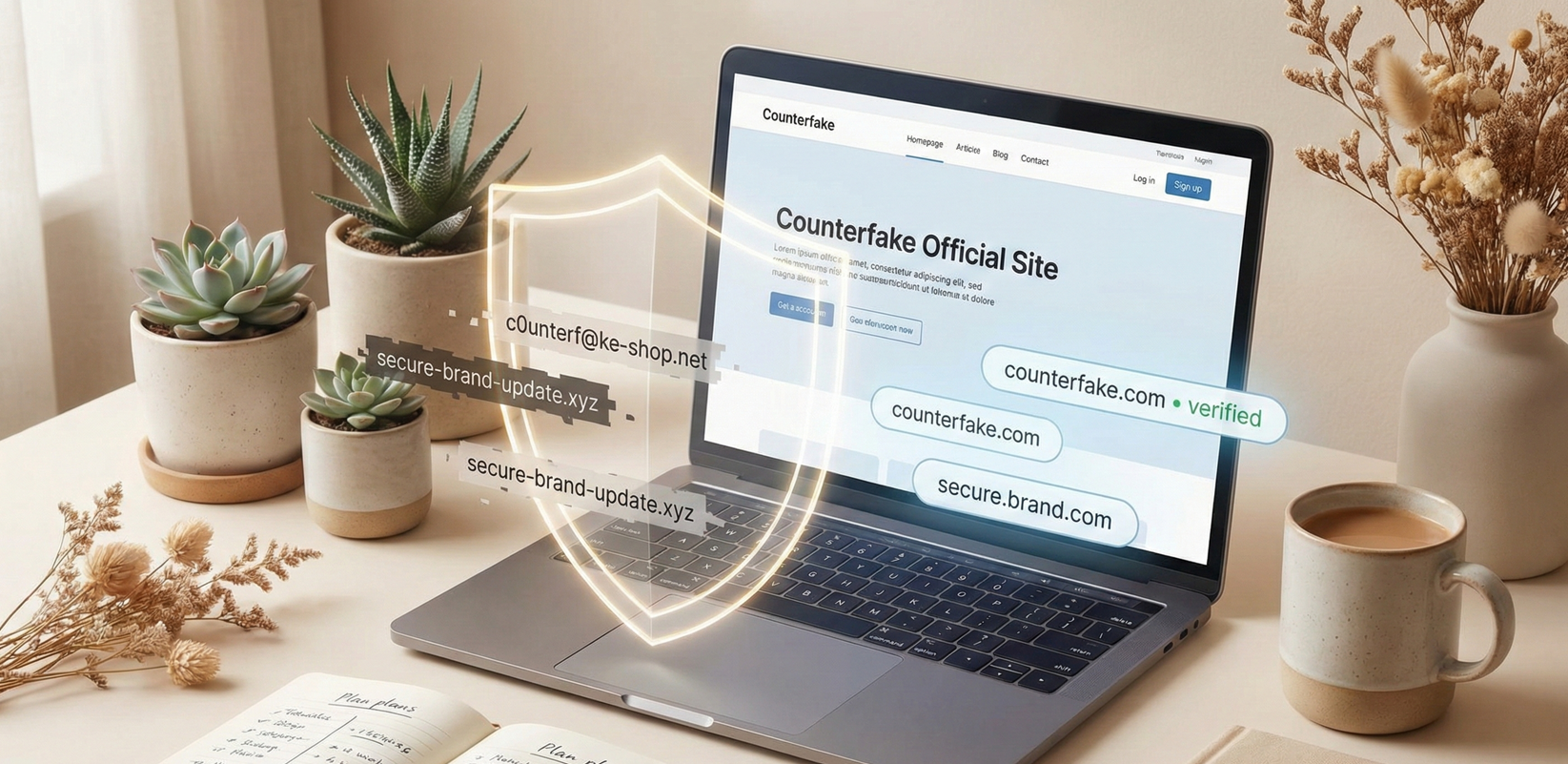
Executive Summary: As we approach 2026, the corporate digital perimeter has dissolved. The threat landscape has shifted away from simple typosquatting toward sophisticated, AI-accelerated domain spoofing designed to deceive even digitally savvy consumers. Today, a lookalike domain is not merely a nuisance redirecting traffic; it is a weaponized entry point for credential harvesting, advanced phishing, and industrial-scale brand counterfeit operations. This guide outlines the mechanics of modern domain deception and articulates why static domain portfolio management is no longer sufficient. Effective digital brand protection now requires autonomous AI systems capable of visually and linguistically analyzing threats across the decentralized web to dismantle fraudulent gateways before they establish trust.
--
The New Vectors of Digital Impersonation
Your domain name is more than a URL; it is the foundational pillar of your digital trust architecture. However, attackers are leveraging increasingly subtle methods to erode that foundation. The era of obvious misspellings (e.g., "https://www.google.com/search?q=Gooogle.com") is ending. The new threat vector relies on cognitive deception and technical obfuscation that traditional firewalls and basic monitoring services miss.
To build a resilient defense, brand leaders must understand the mechanics of the modern attack surface:
1. Homograph Attacks and IDN Spoofing
This is currently one of the most pernicious threats to digital integrity. Attackers utilize Internationalized Domain Names (IDNs) to create domains using characters from different scripts (like Cyrillic or Greek) that look identical to Latin characters in common fonts. For example, using the Cyrillic "а" instead of the Latin "a". To the naked eye—and many basic scanners—the domain appears legitimate. These "evil twins" are primary drivers for phishing campaigns that bypass user scrutiny.
2. Subdomain Hijacking and "Combo-Squatting"
Rather than attacking the main domain name, threat actors are increasingly utilizing "combo-squatting." This involves combining a legitimate brand name with relevant keywords (e.g., "[BrandName]https://www.google.com/search?q=-support.com" or "secure-login-[BrandName].net"). Because these domains contain the exact brand name and sound functionally legitimate, they often evade basic keyword filters and achieve high click-through rates in phishing emails.
3. AI-Generated Phishing Infrastructure
Generative AI has lowered the barrier to entry for creating convincing fake sites. Attackers can now instantly clone your brand’s CSS, HTML structure, and visual assets to create pixel-perfect phishing pages hosted on lookalike domains. In an environment where consumers desperately need a reliable "real or fake brand scanner," attackers are using technology to ensure the fake looks undeniably real.
The Imperative for Proactive Digital Brand Protection
The convergence of these threats means that reactive strategies are obsolete. Waiting for a customer complaint or a dip in revenue before investigating a suspicious domain is a failure of governance.
The financial and reputational ramifications are severe. According to reports analyzed by organizations like the OECD and EUIPO, the trade in counterfeit goods, facilitated by these deceptive online gateways, runs into the hundreds of billions annually. Beyond direct revenue loss from a brand counterfeit, the damage done by a successful phishing attack launched from a lookalike domain—compromising user data and shattering brand trust—can be unrecoverable. The Cybersecurity & Infrastructure Security Agency (CISA) has repeatedly warned that phishing remains a primary access vector for major breaches, often utilizing these spoofed domains to gain initial footholds.
Beyond Traditional Domain Portfolio Management
Historically, corporations practiced defensive registration—buying up common misspellings of their brand. In the face of infinite IDN permutations and combo-squatting options, this approach is financially unsustainable and strategically ineffective.
Modern defense requires moving from passive management to active, AI-driven hunting.
The AI Advantage in Dismantling Threats: Effective protection requires systems that think like an attacker but operate at machine speed. Counterfake’s approach utilizes multi-modal AI that goes beyond textual analysis.
- Visual DNA Analysis: Standard monitoring tools look at DNS records. Advanced AI, however, renders the webpage on a suspicious domain and analyzes it visually. It uses computer vision to identify stolen logos, copied color palettes, and cloned login forms, even if the text has been obfuscated to evade OCR (Optical Character Recognition). This serves as an enterprise-grade alternative to the consumer need for a "fake product checker online."
- Behavioral Heuristics: AI assesses the intent of a domain. Is a newly registered lookalike domain suddenly configuring MX records (indicating an intent to send emails)? Is it utilizing aggressive SEO tactics targeting your brand keywords? These behavioral signals allow for pre-emptive action before a phishing campaign fully launches.
Securing the Future Perimeter
The defense of your brand’s digital gateway is no longer a task for the IT department’s back burner; it is a boardroom imperative critical to maintaining digital integrity. As attackers weaponize AI to create more convincing counterfeits and phishing sites, brands must counter with superior AI that provides persistent, autonomous surveillance. True resilience means ensuring that when a customer steps through a digital door bearing your name, it is the one you built, not a trap set by an adversary.
References:
- Europol & EUIPO. (2023). Intellectual Property Crime Threat Assessment 2023. European Union Intellectual Property Office.
- Cybersecurity & Infrastructure Security Agency (CISA). (2024). Phishing Resistant Multi-Factor Authentication and Domain Security Guidance. U.S. Department of Homeland Security.
- World Intellectual Property Organization (WIPO). (2024). WIPO Overview of WIPO Panel Views on Selected UDRP Questions, Third Edition (WIPO Overview 3.0) - Section on confusing similarity and bad faith registration.
- OECD/EUIPO. (2021). Global Trade in Fakes: A Worrying Threat. OECD Publishing, Paris.