Counterfake Beauty Intelligence Series | Episode 2: Beyond the Hologram: Why Physical Security Fails in a Digital World
Executive Summary
For decades, the cosmetics industry has poured millions of dollars into physical security measures—holograms, complex serial numbers, and custom QR codes—to authenticate their products. However, in the 2026 digital marketplace, these legacy defenses have been rendered dangerously obsolete. "Superfake" manufacturers now possess the technology to replicate sophisticated physical tags within 48 hours, weaponizing consumer trust against the brand itself. Furthermore, physical security features are entirely non-functional in the low-resolution environment of online shopping. This article examines the critical vulnerabilities of relying on physical packaging in a digital-first economy and illustrates how automated brand protection software utilizes advanced computer vision to verify the "digital fingerprint" of a product, ensuring authenticity at the point of digital discovery rather than physical delivery.
--
The modern beauty consumer's journey rarely begins at a physical makeup counter; it begins on a screen. Despite this massive shift to e-commerce and social selling, many brands are still fighting a digital war with physical weapons. The persistent reliance on packaging-based security is not merely an inefficient capital expenditure; it actively creates blind spots that illicit syndicates aggressively exploit.
The Illusion of Physical Security
The fundamental flaw in physical authentication—such as holographic seals, color-shifting inks, or specialized embossing—is that it assumes the consumer has the product in their hands prior to purchase. In the realm of digital commerce, this is never the case.
When a brand introduces a new physical security feature, it inadvertently provides a blueprint for counterfeiters. The illicit manufacturing sector is highly agile. In 2026, the syndicates producing "Superfakes"—counterfeits so precise they deceive even seasoned authenticators—utilize industrial-grade 3D scanners and advanced printing technologies. They routinely reverse-engineer and perfectly replicate a brand's multi-million-dollar hologram initiative within 48 hours of its market debut.
This creates a severe secondary risk: the weaponization of trust. When a consumer receives a toxic, counterfeit serum that features a perfectly forged QR code or holographic seal, their suspicion is entirely disarmed. The fake security element validates the fake product. The consumer uses the hazardous cosmetic with complete confidence, maximizing the potential for biological harm and catastrophic brand damage.
The Low-Resolution Digital Blindspot
Even if a physical security tag cannot be immediately duplicated, it is functionally useless in the primary arena of modern commerce: the digital marketplace.
Consumers make purchasing decisions based on highly compressed JPEGs, fleeting social media stories, and low-light influencer videos. A human moderator, or even a basic trademark-scanning bot, cannot scan a physical QR code embedded in an Instagram Reel. They cannot tilt a digital image to verify the authenticity of a color-shifting hologram. In the digital space, the physical security elements that brands spend millions to develop are entirely invisible.
Because physical security requires physical proximity, it is a reactive measure. It only proves a product is fake after the consumer has been deceived, the transaction has occurred, and the counterfeit has been shipped. In 2026, effective anti-counterfeiting must intercept the threat before the conversion.
The Shift to the "Digital Fingerprint"
To secure the modern supply chain, brands must abandon the reliance on easily copied physical tags and transition to digital integrity verification. This requires deploying autonomous systems capable of analyzing the product exactly as the consumer sees it: through a screen.
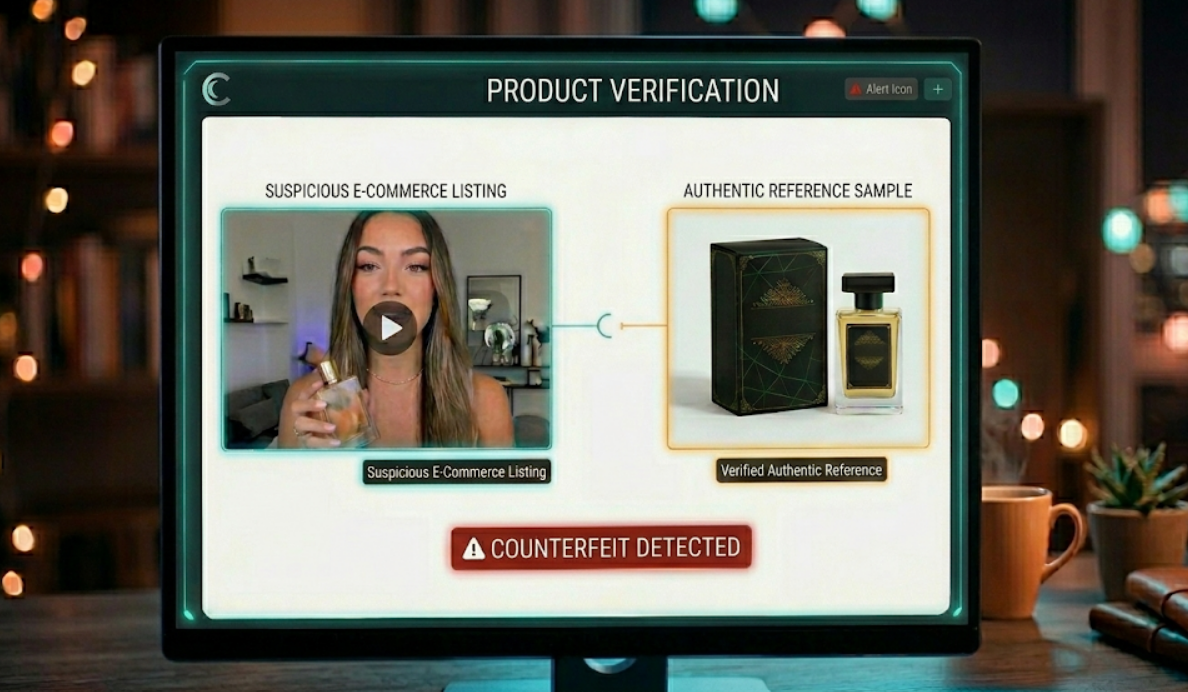
Counterfake’s automated brand protection software fundamentally changes the paradigm. Instead of fruitlessly searching for a physical hologram in a low-resolution image, our proprietary Computer Vision technology scans the "Digital Fingerprint" of the packaging.
Our multi-agent AI is trained on the exact structural and visual parameters of authentic brand assets. When scanning millions of marketplace listings and social commerce feeds, Counterfake does not look for what the counterfeiters added (like a fake QR code); it looks for what they failed to perfect.
By utilizing advanced computer vision to authenticate the digital footprint of a cosmetic product, brands can proactively identify and eliminate superfakes from the internet before a consumer ever clicks "Buy." Transitioning from physical holograms to AI-driven digital verification is not just an upgrade in technology; it is a strategic imperative. It stops the rapid hemorrhage of revenue to illicit syndicates and guarantees that the products reaching your consumers are safe, authentic, and truly representative of your brand's uncompromising standards.
References:
- World Intellectual Property Organization (WIPO): The Transition from Physical to Digital IP Enforcement in the E-Commerce Sector.
- European Union Intellectual Property Office (EUIPO): The Vulnerability of Physical Authentication Elements to Rapid Reverse-Engineering.
- Organization for Economic Co-operation and Development (OECD): Best Practices in Digital Brand Protection and Computer Vision Applications.